Evaluating Upcoming DeFi Projects: A Technical Due Diligence Framework

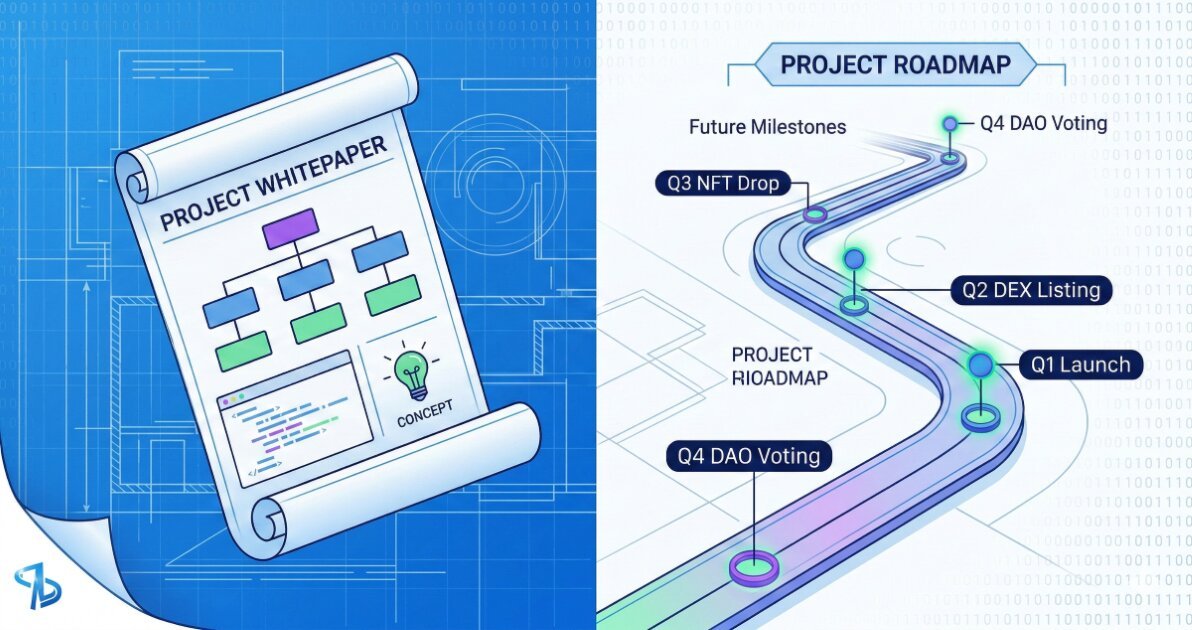
When new DeFi protocols announce launch plans, most coverage focuses on roadmaps and valuations. More useful is a framework for evaluating technical maturity, mechanism design, and operational readiness before mainnet deployment. This article walks through the technical checkpoints that distinguish experimental protocols from production ready infrastructure, using patterns observed across projects that announced 2024 launches.
Smart Contract Maturity and Audit Coverage
Audit reports are table stakes, but audit depth varies. Look for protocols that underwent multiple audits from distinct firms with different specializations: formal verification teams catch logic errors that manual reviewers miss, and vice versa. Check whether audits covered the actual deployed bytecode or earlier versions. Some projects publish audit reports for v1 contracts but deploy v2 with material changes.
Immutable contracts eliminate upgrade risk but lock in any undiscovered vulnerabilities. Upgradeable contracts using proxy patterns add governance risk and complexity. The optimal choice depends on contract complexity and expected iteration speed. Projects deploying novel mechanisms (new AMM curves, liquidation engines, or collateral types) often benefit from upgradeability during the first 6 to 12 months, then transition to immutable deployments once the design stabilizes.
Review the project’s approach to test coverage. Protocols with high unit test coverage (above 95 percent for core logic) and extensive integration tests demonstrate engineering discipline. Fuzz testing and invariant testing catch edge cases that manual test cases miss. Projects that publish their test suites and simulation results provide transparency into failure modes they’ve considered.
Oracle Design and Price Feed Architecture
Oracle failures remain a primary attack vector. Evaluate whether the project uses a single oracle provider or aggregates multiple sources. Single source dependencies create centralization risk and single points of failure. Protocols that aggregate Chainlink, Band Protocol, and protocol owned oracles gain redundancy but must implement median or weighted average logic carefully to prevent manipulation through any single feed.
Check the update frequency and deviation thresholds. Oracles that update only when prices move beyond a threshold (for example, 0.5 percent) reduce gas costs but introduce staleness risk during volatile periods. High frequency trading protocols and liquidation engines need sub minute updates. Lending protocols can often tolerate 15 to 30 minute intervals for collateral valuation.
Time weighted average prices (TWAP) provide manipulation resistance but lag current prices. Protocols using TWAP for critical functions like liquidations must account for this lag in their risk parameters. Some projects implement dual oracle systems: instant prices for user facing displays and TWAP for liquidation triggers.
Liquidity Bootstrapping Mechanisms
How a protocol seeds initial liquidity affects long term stability. Fair launch models that avoid preferential allocations or vesting cliffs reduce governance capture risk but may struggle to attract sufficient TVL. Protocols offering liquidity mining incentives must balance token emissions against sustainable yield.
Examine the emissions schedule. Projects that frontload 60 to 80 percent of token supply in the first year create mercenary capital risk. Users farm, dump, and exit. Longer vesting periods (2 to 4 years) with gradual unlocks encourage participant retention. Calculate the fully diluted market cap at various TVL levels to assess whether the protocol can sustain advertised APYs without relying solely on token emissions.
Bonding mechanisms and protocol owned liquidity reduce dependency on mercenary LPs. Protocols that use a portion of revenue to permanently acquire liquidity (like Olympus DAO pioneered) build resilience against liquidity exits during market stress.
Composability and Integration Surface
DeFi’s value proposition includes composability with existing protocols. Projects launching isolated ecosystems sacrifice integration opportunities. Check whether the protocol uses standard token interfaces (ERC20, ERC4626 for vaults) and whether core functions use common patterns that aggregators and other protocols can integrate without custom adaptors.
Cross chain deployments add complexity. Projects deploying to multiple chains must address bridge security, liquidity fragmentation, and governance synchronization. Canonical deployments on a single chain simplify security but limit market reach. Projects using multichain messaging protocols like LayerZero or Axelar introduce dependencies on those bridge infrastructures.
Evaluate how the protocol handles MEV. Projects building DEXs or lending markets need strategies for managing sandwich attacks and liquidation bots. Some protocols integrate with Flashbots or similar private mempools. Others build auction mechanisms directly into liquidation logic.
Governance Structure and Admin Controls
Review the governance implementation. Projects launching with multisig admin keys concentrate risk in a small set of signers. DAO governance distributes control but moves slowly and faces voter apathy. Hybrid models with guardian multisigs that can pause contracts but not modify parameters offer a middle ground.
Check parameter boundaries. Well designed protocols encode acceptable ranges for critical parameters directly in contracts (for example, interest rate models bounded between 0 and 100 percent). This prevents governance attacks or errors from setting extreme values that break the protocol.
Time locks on governance actions give users notice before changes execute. Standard time locks range from 24 hours to 7 days. Longer time locks provide more exit time but slow protocol iteration. Projects should clearly document which functions have time locks and which admin actions can execute immediately.
Worked Example: Evaluating a Lending Protocol Launch
Consider a new lending protocol launching on Ethereum. The project published two audits: one from a generalist firm and one from a formal verification team. Both covered the current codebase. Test coverage shows 97 percent for core lending logic and 89 percent overall, with integration tests for liquidation scenarios and interest rate edge cases.
The oracle system aggregates three Chainlink feeds with a median calculation. Updates trigger when price deviations exceed 1 percent or every 20 minutes. Liquidation logic uses spot prices but includes a 10 percent liquidation bonus to incentivize fast execution even if prices move between oracle updates.
Initial liquidity comes from a combination of protocol owned liquidity (30 percent of treasury allocated) and liquidity mining with a 4 year emissions schedule releasing 20 percent in year one. Contracts implement ERC4626 for yield bearing tokens, allowing easy integration with aggregators.
Governance starts with a 5 of 9 multisig that can pause contracts and adjust interest rate curves within predefined bounds (0 to 50 percent base rate, 0 to 200 percent slope). Parameter changes have a 48 hour time lock. The roadmap includes transitioning to token based governance after 6 months.
This configuration shows reasonable security practices but retains centralization through the multisig. The 48 hour time lock provides limited exit time for large positions. Users should monitor governance forums and hold only amounts they can withdraw within that window until the protocol proves operational stability.
Common Mistakes and Misconfigurations
- Treating audit reports as binary pass/fail signals. Read the actual findings. High severity items marked as “acknowledged” rather than “fixed” indicate accepted risks.
- Ignoring upgrade paths and proxy patterns. Upgradeable contracts introduce complexity. Verify that upgrade keys use appropriate multisigs or governance, not EOAs.
- Overlooking oracle manipulation surface area. Protocols using low liquidity DEX pools as price sources remain vulnerable to flash loan attacks regardless of TWAP averaging.
- Discounting governance capture in low float launches. Projects distributing small circulating supply create situations where whales can acquire governance control cheaply.
- Assuming cross chain deployments have uniform security. The same protocol deployed on different chains faces different consensus finality times, gas economics, and bridge risks.
- Missing liquidation mechanism testing. Protocols that haven’t simulated liquidation cascades under extreme volatility may fail when first tested by markets.
What to Verify Before You Rely on This
- Current audit status and scope. Confirm audits cover deployed bytecode, not earlier versions. Check if auditors assessed the actual chain deployment or testnet code.
- Oracle data sources and update parameters. Review oracle addresses, update frequencies, and deviation thresholds in the deployed contracts, not just documentation.
- Admin key configurations. Verify the current multisig signers or governance contract addresses. Check if time locks are actually enforced onchain.
- Liquidity depth across relevant trading pairs. Measure actual on chain liquidity, not TVL. Protocols can show high TVL but lack liquid exit paths.
- Token emission schedule and vesting terms. Read the token contract to confirm emissions match announced schedules. Check founder and investor vesting parameters.
- Integration with existing protocols. Test whether aggregators like 1inch or Yearn have integrated the protocol, signaling technical compatibility and baseline security review.
- Historical parameter changes and governance actions. Review governance history for any emergency pauses, parameter changes, or upgrade incidents.
- Bug bounty program scope and payout terms. Active bug bounties with meaningful payout caps indicate ongoing security investment.
- Network and gas cost assumptions. Protocols optimized for L1 may perform poorly on L2s with different gas accounting or vice versa.
Next Steps
- Run a small test transaction on testnet or with minimal mainnet capital. Verify the protocol behaves as documented before committing significant funds.
- Set up monitoring for governance proposals and parameter changes. Subscribe to governance forums and onchain alert services for protocols you use.
- Calculate your personal risk parameters. Define maximum position sizes based on your ability to exit within governance time lock windows and protocol liquidity depth.
Category: DeFi